
How to turn your on-premise Dell Pro Max GB10 into a globally reachable AI workstation — without poking a single hole in your corporate firewall.
The Scene
Picture this. Your Dell Pro Max with GB10 is humming away on your desk — terabytes of NVMe storage, the ARM CPU barely sweating at single-digit memory usage, temperatures cruising in the low 40s°C. You type ollama run against a 120-billion-parameter GPT-OSS model, and within seconds it’s reasoning through machine-learning concepts, streaming markdown tables straight to your terminal.
It’s glorious. It’s local. It’s yours.

The GB10 on a quiet Saturday night — 40°C, 5% memory used, casually reasoning through ML paradigms on a 120B model. Entirely on-prem.
Then you close the lid and walk out of the office.
Suddenly that beast is unreachable. No public IP. No router access. No friendly VPN admin who’ll whitelist you by 5pm. Your GB10 is sitting on a private subnet (something like 192.168.x.x), and your laptop at the cafe has no idea how to find it.
This is the part nobody warns you about when you buy an on-prem AI workstation.
Why the Usual Tricks Don’t Work
If you’ve tried this before, you know the pain:
- Port forwarding on the router — requires admin access most enterprises don’t hand out
- Corporate VPN — your AI workstation rarely qualifies as a “blessed” endpoint
- Tailscale / ZeroTier — excellent, but often blocked at the firewall on corp Wi-Fi
- Ngrok — works, but paid tiers for stable subdomains and TCP tunnels
What we actually want is a persistent outbound tunnel the GB10 maintains itself — because outbound traffic is almost always allowed.
Enter portmap.io
portmap.io is a free port-forwarding and tunneling service that flips the connection model on its head. Your GB10 reaches out to portmap.io’s server and holds open a reverse SSH tunnel. You then connect into that tunnel from anywhere on the planet.
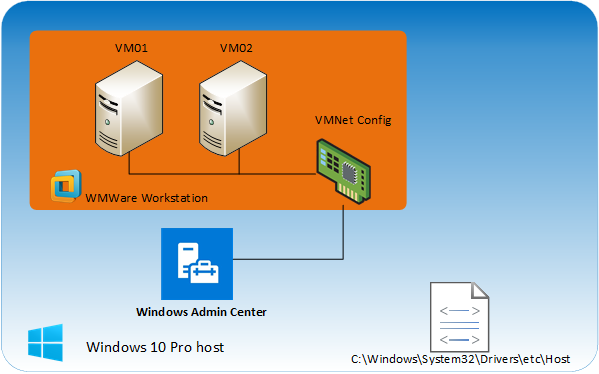
The Architecture
Your Laptop (Cafe) → portmap.io ← Your GB10 (Office) (inbound) (outbound tunnel, firewall-friendly)Because the GB10 initiates the connection outbound on port 22, corporate firewalls treat it like any other SSH session. No inbound rules, no port forwarding, no IT ticket.
Full Setup: From Zero to Remote AI in About 20 Minutes
Part 1 — Prepare the GB10
Step 1: Install and start OpenSSH
bash
sudo apt update && sudo apt install openssh-server -ysudo systemctl enable --now sshsudo systemctl status ssh # look for active (running)Step 2: Note your local username
bash
whoamiSave this — you’ll use it in the final connection command. I’ll refer to it as <gb10user> from here on.
Part 2 — Configure portmap.io
Step 3: Create a free account at portmap.io, verify your email, and log into the dashboard. The username you pick here I’ll call <pmuser>.
Step 4: Create a configuration
In the dashboard:
- Go to Configurations → Create New Configuration
- Name it something memorable like
gb10-ssh - Choose SSH as the protocol
- Click Generate to create your private key
- Download the
.pemfile — you won’t get a second chance
You’ll end up with a key file named along the lines of <pmuser>.gb10-ssh.pem.
Step 5: Create a mapping rule
Go to Mapping Rules → Create New Rule and fill in:
| Field | Value |
|---|---|
| Configuration | gb10-ssh |
| Port on portmap.io | any unused port between 1024–65535 — I’ll call this <tunnel_port> |
| Port on your PC | 22 (the SSH port on the GB10) |
| Allowed IPs | leave blank for now, lock it down later |
Save the rule.
Tip: Pick your
<tunnel_port>randomly. Avoid obvious numbers like2222,22022, or12345— anything scannable invites noise from the internet’s background radiation of bots.
Part 3 — Bring Up the Tunnel
Step 6: Copy the key onto the GB10
bash
mkdir -p ~/.sshmv ~/Downloads/<pmuser>.gb10-ssh.pem ~/.ssh/chmod 600 ~/.ssh/<pmuser>.gb10-ssh.pemThe chmod 600 is non-negotiable — SSH will silently refuse keys with looser permissions.
Step 7: Test the tunnel manually
bash
ssh -i ~/.ssh/<pmuser>.gb10-ssh.pem \ <pmuser>.gb10-ssh@<pmuser>-<tunnel_port>.portmap.io \ -N -R <tunnel_port>:localhost:22Flags:
-N→ no interactive shell, we’re just forwarding-R→ reverse tunnel, exposing local port 22 through portmap
If the command sits there silently with no output, the tunnel is live. Hit Ctrl+C when you’re ready to move on.
Part 4 — Make It Permanent with systemd
Running the tunnel in a terminal window is fine for testing. For production, you want it auto-starting on boot and reconnecting if the network blips.
bash
sudo nano /etc/systemd/system/portmap-tunnel.servicePaste this (substitute your placeholders):
ini
[Unit]Description=Portmap.io SSH Tunnel for GB10After=network.target[Service]ExecStart=/usr/bin/ssh -i /home/<gb10user>/.ssh/<pmuser>.gb10-ssh.pem \ <pmuser>.gb10-ssh@<pmuser>-<tunnel_port>.portmap.io \ -N -R <tunnel_port>:localhost:22 \ -o ServerAliveInterval=60 \ -o ExitOnForwardFailure=yes \ -o StrictHostKeyChecking=noRestart=alwaysRestartSec=10User=<gb10user>[Install]WantedBy=multi-user.targetThen:
bash
sudo systemctl daemon-reloadsudo systemctl enable --now portmap-tunnelsudo systemctl status portmap-tunnelThe ServerAliveInterval=60 is important — it pings the portmap server every minute so NAT tables don’t silently drop the connection mid-siesta.
Part 5 — Connect From Anywhere
From your laptop at the airport, hotel, cafe, wherever:
bash
ssh -p <tunnel_port> <gb10user>@<pmuser>-<tunnel_port>.portmap.ioYou’re in. You’re on the GB10. You can ollama run a 120B model and stream the output back over the tunnel as if you were sitting in front of it.
Real-World Use Cases
Once the tunnel is live, a few things open up:
- VS Code Remote – SSH — install the extension, point it at your portmap host, and edit code on the GB10 like it’s local. Intellisense, debugging, the works.
- Remote Ollama inference — run models on the GB10 but call them from a lightweight laptop. No model weights downloaded, no VRAM pressure on your travel machine.
- Jupyter / API tunneling — forward additional ports (8888, 11434, etc.) through the same SSH connection with
-Lflags for remote notebooks or API access. - Client demos — show a prospective customer what on-prem AI looks like, from their boardroom, without shipping the hardware.
Bonus: SSH from Your Phone
The tunnel doesn’t care what’s on the client side — a phone works just as well as a laptop. For Android, install Termius (the free tier is plenty for a single host). iPhone users: same app, same flow.
In Termius:
- Keychain → + → Generate Key — create a dedicated mobile keypair. Export the public key and append it to
~/.ssh/authorized_keyson the GB10. (Per-device keys matter: if the phone walks off, you revoke just that one line.) - Hosts → + New Host — set:
- Hostname:
<pmuser>-<tunnel_port>.portmap.io - Port:
<tunnel_port> - Username:
<gb10user> - Key: your new mobile key
- Hostname:
- Enable biometric unlock on the Termius keychain. Tap, Face ID / fingerprint, you’re in the GB10 shell.
Pro tip: always connect into a tmux session. Install it once on the GB10 (sudo apt install tmux), then launch your work inside tmux new -s ai. When your phone inevitably drops signal in an elevator, the job keeps running — you just reattach with tmux attach -t ai when you’re back.
What’s actually useful from a phone: kicking off long ollama pull downloads, restarting services, tailing logs with journalctl -u ollama -f, quick health checks with nvidia-smi, and — surprisingly — real inference. Prompting a 120B model from a pocket device while standing in line for coffee is a strange kind of magic.
Security Hardening (Do This Before You Forget)
The setup above works, but it’s internet-exposed. Lock it down:
- Restrict Allowed IPs in the portmap.io mapping rule — limit to your home, office, or phone-tether public IP.
- Disable password SSH auth on the GB10. Key-based only:
bash
sudo sed -i 's/^#*PasswordAuthentication.*/PasswordAuthentication no/' /etc/ssh/sshd_config
sudo systemctl restart ssh- Install fail2ban — it’s a one-liner and it catches the inevitable brute-force probes:
bash
sudo apt install fail2ban -y- Rotate the portmap key every few months. Revoke old configurations in the dashboard.
- Log your tunnel uptime — if
portmap-tunnel.servicestarts flapping, something upstream changed.
Wrapping Up
The GB10 is a serious piece of hardware — serious enough that keeping it chained to a single physical location feels like a waste. A 20-minute portmap.io setup turns it into something closer to what it should be: a always-on, always-reachable AI workstation you can hit from any device, anywhere, without begging IT.
The screenshot at the top of this post was taken over exactly this kind of setup. The terminal was miles from the machine. The model was running locally on the GB10. The tunnel just worked.
Go build something.
⚠️ Disclaimer
This guide describes a lab and proof-of-concept setup — the kind of configuration suited to an internal AI development team that needs quick, friction-free access to their own GB10 for experimentation, model testing, and rapid iteration.
It is not a production-grade remote access pattern for corporate environments. Routing traffic through a third-party tunneling service, even securely, sidesteps the network controls your organization has in place for good reason: data loss prevention, egress monitoring, identity governance, auditable access trails, and compliance posture (ISO 27001, SOC 2, PCI, regional data residency rules, etc.).
Before doing anything like this on a corporate network or with corporate data:
- Consult your SOC (Security Operations Center) or InfoSec team first
- Review your organization’s acceptable use, remote access, and third-party service policies
- Consider enterprise-sanctioned alternatives: Zero Trust Network Access (ZTNA), identity-aware proxies, bastion hosts, corporate VPN with MFA, or vendor-supported remote management tooling
- For regulated industries (finance, healthcare, government), assume the answer is no until legal and compliance explicitly say otherwise
Use your judgment. What’s perfectly fine for a home lab or a sandboxed dev environment can become a career-limiting event on a production network.

Leave a Reply